Introduction
Recently AWS have announced a major change to pricing for a crucial part of most organisations infrastructure. Whereas previously you were not charged for IPV4 addresses that were in use, from February 1st 2024 you will start being billed.
Below is a link with more information from AWS:
https://aws.amazon.com/blogs/aws/new-aws-public-ipv4-address-charge-public-ip-insights/
How will this effect me?
For each public IPV4 address you have assigned you will be billed an additional $4 per month, so a bit more than $40pa. This might not sound like a lot, but these costs can add up quickly if you are not observant. For example lets consider the below infrastructure:
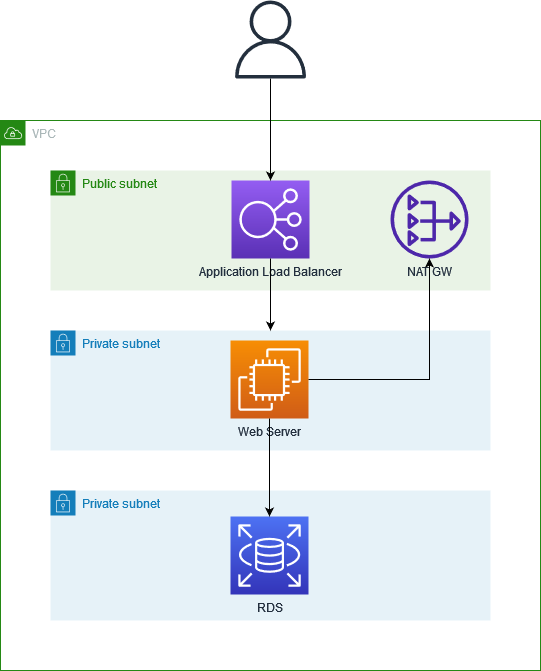
We have the following resources deployed that could potentially have a public IPV4 address:
Elastic Load balancer – This needs an IPV4 address per Availability Zone (AZ), and will need to be in at least 2 AZs
NAT Gateway – This provides connectivity to the internet for the resources in private subnets, and will need an IPV4 address per AZ.
EC2 instance – This diagram has the EC2 instance sitting in a private AZ so it doesn’t need a Public IP attached, but often customers will have added one accidentally.
RDS – This diagram has the RDS database in a private public, but as with the EC2 instance often customers have accidentally configured the RDS service with a public ip that wont be used
There are other services that would possibly be effected, for example you may be using ECS tasks with public IPV4 address attached.
How can I avoid this cost?
For many customers the answer will likely be that you can’t avoid it altogether, however you can likely optimise your usage of AWS to reduce the impact. Below are some examples:
Check for wastage:
Firstly ensure you don’t have Elastic IP’s sitting around unused! You get charged for these currently, so its a good idea to do this sooner rather than later. Do you have Public IP’s on resources that don’t need them such as private RDS/EC2? If so you should review if these can be removed.
Consolidate resources:
Are you running multiple Elastic Load Balancers in the same VPC? You can often consolidate these down and use path based routing to point to separate services that you are running.
Managed NAT:
If you are running multiple AWS accounts then you may want to review whether a centralised egress works better for you, where you run one Managed NAT for several workloads
Conclusion
There is plenty of time to review your AWS infrastructure to reduce the impact of this change, and many of the efficiencies you can put in place will help reduce your bill immediately. If you aren’t comfortable making these changes yourself or you need help reviewing your options then get in touch with Rochwall and we will be happy to help
